
SEC301 & GISF
Reviewing the SANS Introductory Course & Its Companion GIAC Certification
 GISF Certified
GISF Certified GIAC Advisory Board
GIAC Advisory BoardCourse at a Glance
Overview
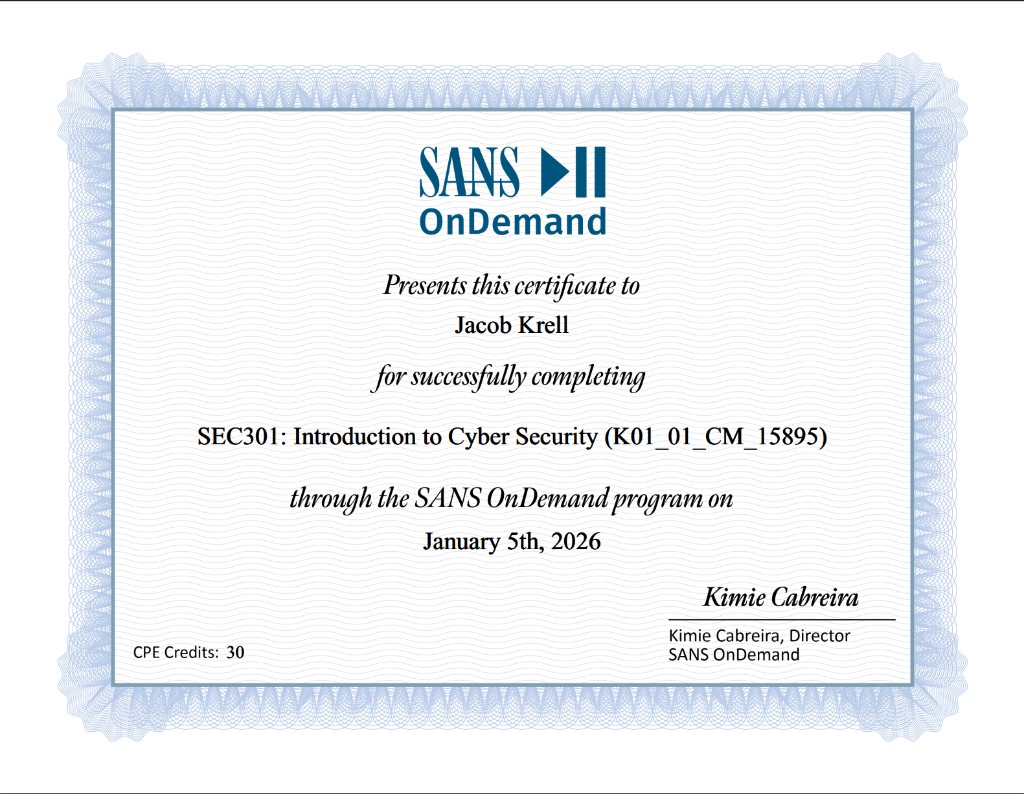
I recently had the opportunity to beta test SEC301: Introduction to Cyber Security from SANS and sit for the paired GIAC Information Security Fundamentals (GISF) certification exam. This review covers both the course and the certification, since SANS and GIAC design them as a unified learning and validation experience.
I came away highly impressed. The course delivers a broad, well structured survey of the cybersecurity landscape with notably current material covering AI generated malware, deepfake phishing, and the evolving threat environment. The GISF certification validates that foundational knowledge across 12 official domains, and the exam itself is a fair, open book assessment that rewards preparation and structured notes.
The online SANS OnDemand platform worked perfectly without any real technical troubles. Everything felt professional, dense with useful information, and well produced. For those seeking a structured, modern, and intellectually solid introduction to cybersecurity, SEC301 paired with the GISF delivers exactly what it promises.
Part 1: The Course (SEC301)
Course Review
SEC301 leans intentionally toward the academic and conceptual side of cybersecurity. Rather than diving deep into implementation details, it focuses on ensuring learners understand what key concepts are and how to recognize them. For example, the course explains and contextualizes attacks like XSS without delving into exploit development or low level mechanics. This approach makes the content accessible, effective for building foundational understanding, and avoids overwhelming the learner with unnecessary technical depth.
The instructor, Rich Greene, was exceptional. The delivery was clear, confident, and engaging, with minimal verbal distractions and a dynamic presentation style that made it easy to stay focused and absorb the material. I also appreciated having both a high quality physical course book and the video instruction. The labs were thoughtfully designed, encouraging critical and abstract thinking while avoiding the trap of excessive CLI commands or implementation minutiae.
Overall, based on the beta version I took, SEC301 serves as an excellent cornerstone for anyone looking to enter cybersecurity or formalize their foundational knowledge. It provides a strong launch point into specialization areas such as penetration testing or incident response, as well as into more technically and operationally intensive certifications. Conceptually, it fits neatly between a CompTIA Security+ and a CISSP-level perspective, and feels roughly comparable in scope to CompTIA's SecurityX exam.
Section by Section Breakdown
Section 1: Cybersecurity Foundation
| Module | Duration |
|---|---|
| 1.1 What Is Cybersecurity? | 49m |
| 1.2 Why It Matters - Business, Personal, and National | 20m |
| 1.3 Risk Basics - Threats, Vulnerabilities, and Impact | 56m |
| 1.4 Vulnerability Management | 37m |
| 1.5 Legal Considerations | 58m |
| 1.6 Compliance Frameworks Overview | 53m |
| 1.7 E-Discovery & Incident Reporting | 23m |
This section opens the course by defining cybersecurity and establishing why it matters across business, personal, and national contexts. It then moves into risk fundamentals, covering the relationship between threats, vulnerabilities, and impact before introducing vulnerability management practices. The section dedicates significant time to the legal landscape, compliance frameworks such as NIST, ISO 27001, HIPAA, and PCI-DSS, and the intersection of electronic discovery with incident reporting.
Starting with legal and compliance is a strong choice, as it situates the topics taught throughout the course, and cybersecurity as a whole, within the correct framework. Understanding the regulatory and legal landscape first gives every subsequent technical concept practical grounding.
The risk basics and vulnerability management content was familiar territory for me, but it should be given my existing CISSP and SecurityX certifications. For someone entering the field, this section lays the essential groundwork.
Section 2: Building Digital Trust: Cryptography, Identity, and Access
| Module | Duration |
|---|---|
| 2.1 The Purpose of Cryptography | 1h 12m |
| 2.2 How Encryption Works | 1h 22m |
| 2.3 Digital Trust - HTTPS, Certificates, Let's Encrypt | 1h 21m |
| 2.4 Identity - Users, Devices, and Trust Anchors | 38m |
| 2.5 Access and Control - AAA | 1h 4m |
| 2.6 Modern Access - SSO, MFA, and Passkeys | 53m |
| 2.7 Protecting Information - The Role of DLP | 18m |
The heaviest section of the course at over six and a half hours, Section 2 covers the full trust stack: what cryptography is and why it matters, how symmetric and asymmetric encryption actually work, how HTTPS and certificates create digital trust through PKI and certificate authorities like Let's Encrypt, and how identity and access control mechanisms such as AAA, SSO, MFA, and Passkeys enforce that trust in practice. It closes with Data Loss Prevention (DLP) principles and their role in protecting sensitive information.
The cryptography coverage stays at the appropriate high level, introducing the ideas without getting bogged down in mathematics. For a foundational course like this, that is exactly the right level of complexity.
The modern access module covering SSO, MFA, and Passkeys felt extremely up to date and highly relevant. Many courses I have taken felt like their identity and access concepts were slightly outdated compared to how enterprises actually operate today, but SEC301 does not have that problem.
Section 3: Understanding Networks and Data in Motion
| Module | Duration |
|---|---|
| 3.1 Network Models & Data Flow | 58m |
| 3.2 IP Addressing, Routing, and Local Communication | 1h 15m |
| 3.3 DNS and Name Resolution | 41m |
| 3.4 Web Communication on the Network | 48m |
| 3.5 Network Security Technologies | 42m |
| 3.6 Network Design Principles | 26m |
| 3.7 Zero Trust Network Architecture | 42m |
Section 3 covers the mechanics of how data moves across networks. It starts with the OSI and TCP/IP models, moves into IP addressing, routing, and local communication, then covers DNS resolution and how web traffic traverses the network. The section shifts to defense with network security technologies such as firewalls, IDS/IPS, and segmentation strategies, covers network design principles, and closes with a dedicated module on Zero Trust Network Architecture.
Rich did an excellent job keeping the networking content engaging. It was in-depth enough to give a foundational understanding for the learner, while not reaching CCNA levels of depth by going into spanning tree protocol and similar implementation details.
I enjoyed the inclusion of Zero Trust Architecture as I think it is an increasingly important aspect of security and will be highly relevant going into the future. Its presence here reinforces the course's commitment to covering what matters now, not just what has traditionally been taught.
Section 4: Modern Attack Tactics: From Phishing to AI-Powered Threats
| Module | Duration |
|---|---|
| 4.1 Getting In: How Attackers Gain a Foothold | 1h 32m |
| 4.2 Wireless Weaknesses: Attacks in the Air | 50m |
| 4.3 Malware in Motion: From Infection to Control | 1h 41m |
| 4.4 Smarter Attacks: AI, Deepfakes, and the New Frontier | 59m |
| 4.5 Mapping the Enemy: Frameworks and Adversaries | 1h 23m |
Section 4 is where the course turns to the offensive side of cybersecurity. It covers how attackers gain initial access through phishing, social engineering, and credential attacks, then examines wireless attack vectors and the full malware lifecycle from infection through command and control. The section stands out with its coverage of AI powered threats including deepfake phishing and AI generated malware, before closing with a detailed look at adversary frameworks like MITRE ATT&CK for mapping and anticipating attacker behavior.
The attack content is appropriately scoped for beginners, focusing on what attacks are and how to recognize them as classes of threats rather than how to actually execute them. Like the rest of the course, this section prioritizes the academic understanding of cybersecurity over operational knowledge.
The MITRE ATT&CK mapping and AI/Deepfakes modules were standout topics for the entire course. In my own professional career, I have leveraged MITRE more than I can count and find it to be one of the greatest resources available to security professionals. Deepfakes are increasingly relevant, and certainly something every cybersecurity professional should be aware of. These modules speak to the modernness and up-to-date nature of the course.
Section 5: Cyber Security Technologies and Web Security
| Module | Duration |
|---|---|
| 5.1 Web Security Awareness | 1h 7m |
| 5.2 Security Toolkits for the Modern Defender | 49m |
| 5.3 Roles in a Security Ecosystem | 1h 15m |
| 5.4 Cloud Security Fundamentals | 43m |
| 5.5 IoT, OT, and ICS | 41m |
| 5.6 Revisiting DLP and SSO | 18m |
| 5.7 Artificial Intelligence in Cybersecurity | 59m |
The final section brings everything together by covering the technologies and roles that make up the modern security ecosystem. It opens with web security awareness, including common vulnerabilities like XSS, CSRF, and injection attacks, then surveys the defensive toolkit available to practitioners. A substantial module on roles within cybersecurity introduces the various career paths and specializations. The section also covers cloud security fundamentals, IoT/OT/ICS security considerations, revisits DLP and SSO in a broader context, and closes with a future focused module on artificial intelligence in cybersecurity.
I liked the inclusion of the Roles in a Security Ecosystem module as it introduces specialization early, allowing the spark of interest to form in the learner that will guide them into selecting a specialization later. It also shows cybersecurity in the real world, which I think is very important for new practitioners.
The AI in Cybersecurity module is a survey of the topic for sure. There are no instructions on how to actually run AI agents or anything like that, but it does a good job introducing the concepts for academic understanding and gives guidance for the learner to dive more deeply into the topic at later times.
Labs
There were many labs provided throughout the course, covering nearly all of the content presented across all five sections. The labs were formatted in such a way as to promote learning through open ended questions and answers rather than rigid, guided walkthroughs. This is an important distinction: rather than asking you to type a specific command and observe the output, the labs encourage you to think critically about the concepts and apply them abstractly.
Each lab was excellently walked through in the video course by Rich Greene, ensuring learners understood not just the answers, but the reasoning behind them. This approach reinforced the course's academic philosophy and kept the exercises grounded in the material without devolving into excessive CLI commands or implementation minutiae. For a foundational course, this is the right balance.
Part 2: The Certification (GISF)
Certification Overview
The GIAC Information Security Fundamentals (GISF) certification is the exam paired with SEC301. It validates a practitioner's knowledge of security foundations, computer functions and networking, introductory cryptography, and cybersecurity technologies. GISF holders demonstrate key concepts of information security including understanding the threats and risks to information resources and identifying best practices to protect them.
According to GIAC, the GISF certification is designed for the following audiences:
- Anyone new to cybersecurity who needs an introduction to security fundamentals
- Non-IT security managers
- Professionals with basic computer and technical knowledge
- Career changers to cybersecurity
- Managers, information security officers, and system administrators
- Anyone who writes, implements, or must adhere to enterprise security policy
"The GISF is powerful because it gives newcomers and cyber-adjacent professionals a shared language with the people doing the work. It connects the dots between threats, networks, identity, cryptography, and risk so you're not just hearing terms, you actually understand how they fit together. Whether you're stepping into cybersecurity or working alongside it, GISF builds the confidence to ask smarter questions and make better decisions. It turns security from something mysterious into something you can reason through and contribute to."
Rich Greene, SANS Certified Instructor
Exam Format & Objectives
GISF Exam Format
- Questions: 75
- Time Limit: 2 hours
- Passing Score: 69%
- Format: Open book, proctored
- Delivery: Remote via ProctorU or onsite via PearsonVUE
- CPE Credits: 30
- Activation Window: 120 days from activation to complete the attempt
GISF Exam Objectives
The GISF exam covers 12 official certification objective domains. Each maps directly to content covered across the five sections of SEC301:
Analyze, document, and anticipate adversary behavior using standardized intelligence models and threat mapping tools.
Identify and apply modern defensive technologies, leveraging automation and AI to enhance security operations.
Understand how cryptography enables trust, privacy, and authenticity across the digital environment.
Demonstrate understanding of cybersecurity, why it matters, and risk fundamentals.
Understand how devices find each other, exchange data, and support web communication on local and global networks.
Understand how identity and access mechanisms apply trust, and how DLP principles protect sensitive data.
Understand how attackers penetrate defenses and establish persistence within a target environment.
Apply practical methods for reducing risk, as well as the frameworks, laws, and ethical principles that shape operations.
Architect and secure networks that protect data, users, and devices in modern distributed environments.
Understand post-exploitation tactics and technological innovations that enhance attacker sophistication.
Secure distributed, cloud-based, and connected environments while maintaining data protection.
Understand fundamental web security risks and how different professional roles maintain organizational security posture.
Exam Experience & Tips
The exam questions tracked nearly exactly to those of the practice tests and the concepts presented in the course. The course quizzes very much fully cover the content on the exam, so if you are doing well on those, you should feel confident going in.
Honestly, the exam felt more like an information lookup exercise than a test of deep understanding. The time allotted per question would allow a person unfamiliar with the material to still pass if they possessed a strong index and ability to look up information quickly. The fact that the exam is open book with generous time per question trains the tester's ability to find information as much as their actual understanding of the topics.
Some questions were fill in the blank, requiring the exact vocabulary usage as that in the book. Even though I knew the answer to many of these, I found myself looking it up anyway to ensure I had the exact word the test was looking for. The exam certainly focuses on the academic side of things, feeling more like a university test than something like the OSCP, CCNA, or other operator focused certifications. It falls in line with the generalized cybersecurity certifications I have taken, like the CISSP and SecurityX, in that regard.
My advice for someone preparing is to use the course books heavily as notes, composing quick lookup indexes prior to the test. Use your time to look up anything you are not completely sure about. You are given plenty of time, and I was just using the default table of contents. If you have gone through the course and done sufficient prep work knowing where to find information in the textbooks, there is little reason to be overly worried about the test.
I took the exam in person at my local community college through PearsonVUE and thought the experience was fine. Check-in was quick and the testing room was quiet and adequate for testing. I did feel a little conspicuous flipping back and forth through all the course texts for so many of the questions, however. Remote proctoring through ProctorU is also available if you prefer to test from home.
GIAC Advisory Board Invite
I scored well enough on the GISF exam to be invited to join the GIAC Advisory Board after about a month of learning. It is worth noting that I already hold the CISSP and CompTIA SecurityX certifications, so I was very familiar with the exam material going in. Your mileage may vary depending on your prior experience.
Comparisons & Recommendations
How SEC301/GISF Compares
Having taken several foundational and advanced cybersecurity certifications, here is how I would position SEC301 and the GISF relative to other well-known options:
| Certification | Focus | How SEC301/GISF Differs |
|---|---|---|
| CompTIA Security+ | Broad operational security fundamentals | SEC301 is more academic and conceptual; Security+ is more implementation focused with performance based questions |
| (ISC)2 CISSP | Senior-level security management and architecture | Similar breadth of topics but CISSP assumes years of experience; SEC301 is designed for newcomers |
| CompTIA SecurityX | Advanced security practitioner, expert level | Comparable conceptual scope, but SecurityX assumes deep practitioner experience; SEC301 teaches the same concepts at an introductory level |
| SANS SEC401 / GSEC | Security essentials with practical depth | The natural next step within the SANS ecosystem; SEC401 builds on SEC301 with significantly more technical depth and operational focus |
If you are completely new to cybersecurity, SEC301 is the right starting point within the SANS curriculum. If you already have operational experience or hold certifications like Security+ or CySA+, you may find the content familiar and could consider starting directly with SEC401 instead.
Who Is This For?
Beyond the official GIAC audience listed in the Certification Overview above, I would add from my experience that SEC301 is also well suited for recent graduates looking to formalize foundational knowledge, and for IT professionals looking to pivot into security. The academic approach of the course makes it particularly effective for people who learn best through structured, concept driven instruction rather than practical labs.
If you already hold certifications like the CISSP, SecurityX, or have significant operational experience, the content will be familiar. However, the SANS delivery and Rich Greene's instruction may still be worth experiencing. For those earlier in their journey, SEC301 provides a strong launch point into specialization areas such as penetration testing, incident response, cloud security, or security architecture.
Final Verdict
SEC301 is a fantastic course and the instructor truly made it. Rich Greene's delivery elevated what could have been a dry survey course into something genuinely engaging and easy to absorb. The material is modern, the platform is polished, and the content is dense with useful information without being overwhelming. For anyone looking to build a solid cybersecurity foundation or formalize knowledge they have picked up on the job, SEC301 paired with the GISF certification is an excellent place to start.
Ready to get started? Check out SEC301 on the SANS website and the GISF certification page.
Verify my GISF certification on Credly.
